Ever since we started working on our own operating system, we’ve encountered numerous myths that significantly hinder the adoption of new technologies. Fortunately, it’s not so difficult to provide compelling evidence that these myths are just that: myths. In this post, we address some of the most common misconceptions.
Myth 1: current operating systems can already handle all the latest challenges
We’ve been hearing people say “we don’t need another OS” for more than 20 years. However, for all this time, mainstream operating systems have continued to suffer from the same three problems:
- Cyberthreats: in 2022, Kaspersky’s security systems detected over 400,000 new malicious files Windows remains the primary target (accounting for 85% of threats), but the number of threats for Linux and Android is steadily increasing (with a 20% and 10% rise, respectively, last year).
- Instability: the infamous Windows blue screen of death still haunts our workdays. If anyone thinks things are different with Linux, they’re mistaken — it also has a screen of death, only it’s black (and it’s known as kernel panic).
- Mutual incompatibility: every year, we’re surrounded by more and more smart devices. According to analysts, by 2025, the number of connected devices worldwide will reach 27 billion. Sometimes, devices produced by one and the same company may run on different operating systems. Consequently, software developers often have to put tremendous effort into adapting the same applications for different OS environments.
Here at Kaspersky we found the solution to these problems by creating KasperskyOS. It’s based on the microkernel concept, the MILS architectural approach, and FLASK architecture.

Average daily number of malicious files detected by Kaspersky security solutions from 2019 to 2022
Myth 2: the cybersecurity advantages of microkernels haven’t been proven
It’s not easy to compare which architecture is better — microkernel or monolithic kernel. However, there have been many serious studies dedicated to this. From these, it’s become evident that:
- Approximately 95% of critical vulnerabilities in Linux and exploits targeting this system wouldn’t be critical in microkernel operating systems.
- Approximately 55% of these critical vulnerabilities could have been mitigated through microkernel verification.
- Approximately 30% could simply have been prevented entirely by implementing a microkernel architecture.
Myth 3: microkernel OS is slow
The performance of an operating system during processes requiring connections to remote desktops is an important concern. Therefore, we paid particular attention to it. And thanks to multicore and codec support, we managed to achieve a level of performance comparable to Linux.
Games are some of the most performance-demanding applications, so as part of our testing we set ourselves the task of running a recently released game that uses GPU heavily on KasperskyOS. This doesn’t mean we’re going to start developing games or consoles. But this experiment did let us clearly demonstrate to our partners which will develop devices on KasperskyOS the system’s real capabilities of performing tasks related to design and 3D modeling.
Myth 4: Linux containers can perform the same tasks that KasperskyOS can using MILS.
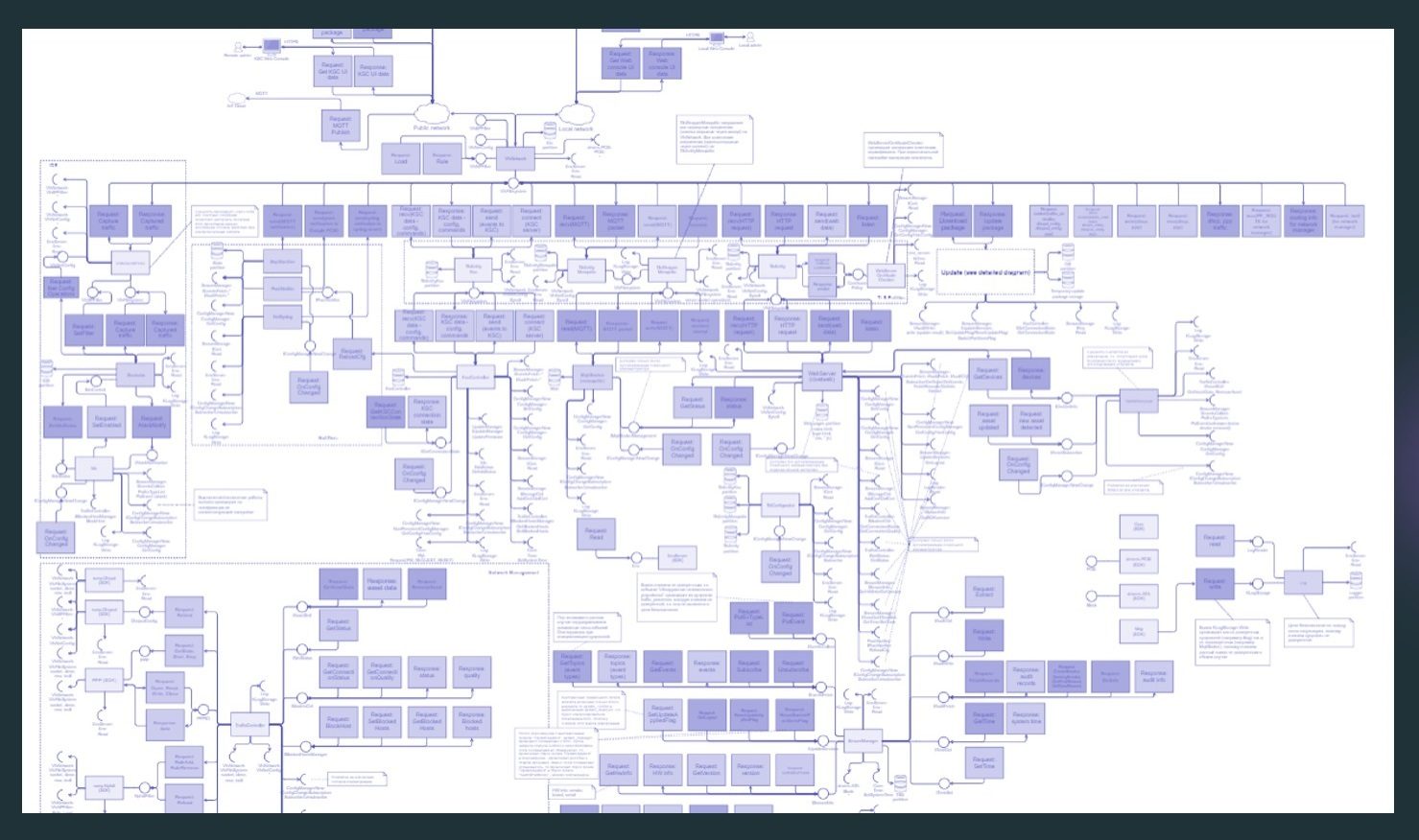
If we look closely at the architecture of our Cyber Immune gateway (one of the first KasperskyOS-based devices to hit the market), we find there around 200 security domains. If we tried to build the same thing on Docker containers in Linux, it would require more than 5GB of RAM. Such a gateway implemented in the form of 200 containers on low-spec hardware with a single-core processor would work extremely slowly. The fundamental difference lies in the approaches: in Linux containers, we essentially take a complete system and trim off what we don’t need, whereas in KasperskyOS, we build it from the ground up with only the necessary components. This significantly optimizes resource consumption.
Myth 5: you can’t build dynamic systems with FLASK
The FLASK concept provides control over security domains using security policies. There is a common belief that this approach makes it impossible to expand OS functionality through applications. However, the evolution of specific products based on KasperskyOS clearly demonstrates the opposite:
- In 2021, we proved with our IoT gateway the possibility of creating KasperskyOS-based Cyber Immune solutions with fixed functionality.
- In 2022, using a thin client as an example, we demonstrated the ability to create Cyber Immune solutions with support for a graphical user interface. Moreover, the partner with which we implemented this project added their own applications to KasperskyOS’s thin client functionality without any hitches.
- We’re currently in the third evolutionary stage — where external developers can create certain types of applications for KasperskyOS. To facilitate this, we’re developing our own application distribution system. The first Cyber Immune platform capable of accepting such applications will be the gateway — since it must be able to connect to a wide range of different devices.
However, we’re not stopping there; we’re now working to transition to the next stage, where on the basis of KasperskyOS it will be possible to create full-fledged Cyber Immune platforms and systems with a large number of applications. Mobile devices are an example of such systems.
Myth 6: development is narrowly specialized
It might seem that development of a new operating system requires developers to completely retrain. But that’s not the case. KasperskyOS is already bringing together developers from entirely different paradigms who use the tools they’re familiar with.
Web applications are being developed for gateways and thin clients utilize the Qt framework, popular in the Linux community. For controllers, there’s nothing preventing the creation of console applications familiar to almost every programmer from their student days.
Furthermore, together with colleagues working on developing an automotive gateway, we offer the option to use standard frameworks from the automotive industry, such as AUTOSAR Adaptive. We’re actively working on providing Flutter technology capabilities in our OS, which will ensure compatibility with Android applications.
Myth 7: the difficulty of porting to different hardware platforms
Some developers fear that developing new operating systems is pointless because drivers are only written for mainstream OS (Linux, Android, Windows). Therefore, any new OS will only work with a limited range of hardware. Understanding this, we launched a research project with the goal of creating technology that enables Linux drivers to run on KasperskyOS with minimal modifications — Linux Compat.
The idea is simple: in KasperskyOS, you can run a piece of code in the secure domain like in a container. We add a thin software layer to this container so the Linux driver thinks it’s operating in its familiar Linux environment. Thanks to this technology, we’ve ported around 300,000 lines of Linux code to KasperskyOS — changing less than 5%. 300,000 lines of code is 8–10 years of work for an experienced developer (when it comes to driver development). Now for some concrete numbers. For example, accelerometer and gyroscope drivers in Linux contain about 7000 lines of code. To run this code using our technology on KasperskyOS, only 20 lines needed to be modified. And the NFC driver, used to support equipment with which mobile devices interact with payment terminals, contains about 1200 lines of code; with our technology, this driver ran without any changes at all.
In my opinion, we’ve developed a technology that will allow us to upscale in the future. And right now we’re choosing the product on which we can fully test this technology.
Everybody needs to choose for themselves whether they want to be mired in myth or in the new Cyber Immune reality. You can learn more on our KasperskyOS website and in blog on Cyber Immunity.
Let’s debunk myths together: reality is way more interesting!
 cyberimmunity
cyberimmunity


 Tips
Tips