Data theft definition
Data theft – also known as information theft – is the illegal transfer or storage of personal, confidential, or financial information. This could include passwords, software code or algorithms, and proprietary processes or technologies. Data theft is considered a serious security and privacy breach, with potentially severe consequences for individuals and organizations.
What is data theft?
Data theft is the act of stealing digital information stored on computers, servers, or electronic devices to obtain confidential information or compromise privacy. The data stolen can be anything from bank account information, online passwords, passport numbers, driver's license numbers, social security numbers, medical records, online subscriptions, and so on. Once an unauthorized person has access to personal or financial information, they can delete, alter, or prevent access to it without the owner’s permission.
Data theft usually occurs because malicious actors want to sell the information or use it for identity theft. If data thieves steal enough information, they can use it to gain access to secure accounts, set up credit cards using the victim’s name, or otherwise use the victim’s identity to benefit themselves. Data theft was once primarily a problem for businesses and organizations but, unfortunately, is now a growing problem for individuals.
While the term refers to 'theft', data theft doesn't literally mean taking information away or removing it from the victim. Instead, when data theft occurs, the attacker simply copies or duplicates information for their own use.
The terms 'data breach' and 'data leak' can be used interchangeably when discussing data theft. However, they are different:
- A data leak occurs when sensitive data is accidentally exposed, either on the internet or through lost hard drives or devices. This enables cybercriminals to gain unauthorized access to sensitive data without effort on their part.
- By contrast, a data breach refers to intentional cyberattacks.
How does data theft happen?
Data theft or digital theft occurs through a variety of means. Some of the most common include:
Social engineering:
The most common form of social engineering is phishing. Phishing occurs when an attacker masquerades as a trusted entity to dupe a victim into opening an email, text message, or instant message. Users falling for phishing attacks is a common cause of data theft.
Weak passwords:
Using a password that is easy to guess, or using the same password for multiple accounts, can allow attackers to gain access to data. Poor password habits – such as writing passwords down on a piece of paper or sharing them with others – can also lead to data theft.
System vulnerabilities:
Poorly written software applications or network systems that are poorly designed or implemented create vulnerabilities that hackers can exploit and use to steal data. Antivirus software that is out of date can also create vulnerabilities.
Insider threats:
Employees who work for an organization have access to customers’ personal information. Rogue employees or disgruntled contractors could copy, alter, or steal data. However, insider threats are not necessarily restricted to current employees. They can also be former employees, contractors, or partners who have access to an organization's systems or sensitive information. Insider threats are reportedly on the rise.
Human error
Data breaches don’t have to be the result of malicious actions. Sometimes they can be the result of human error instead. Common errors include sending sensitive information to the wrong person, such as sending an email by mistake to the incorrect address, attaching the wrong document, or handing a physical file to someone who shouldn't have access to the information. Alternatively, human error could involve misconfiguration, such as an employee leaving a database containing sensitive information online without any password restrictions in place.
Compromised downloads
An individual might download programs or data from compromised websites infected by viruses like worms or malware. This gives criminals unauthorized access to their devices, allowing them to steal data.
Physical actions
Some data theft is not the result of cybercrime but physical actions instead. These include the theft of paperwork or devices such as laptops, phones, or storage devices. With remote working increasingly widespread, the scope for devices to go missing or be stolen has also increased. If you’re working in a public place such as a coffee shop, someone could watch your screen and keyboard to steal information like your login details. Card-skimming – where criminals insert a device into card readers and ATMs to harvest payment card information – is another source of data theft.
Database or server problems
If a company storing your information is attacked because of a database or server problem, the attacker could access customers' personal information.
Publicly available information
A lot of information can be found in the public domain – i.e., through internet searches and looking through user posts on social networks.
What types of data are typically stolen?
Any information stored by an individual or organization could be a potential target for data thieves. For example:
- Customer records
- Financial Data such as credit card or debit card information
- Source codes and algorithms
- Proprietary process descriptions and operating methodologies
- Network credentials such as usernames and passwords
- HR records and employee data
- Private documents stored on computer computers

Consequences of data theft
For organizations that suffer a data breach, consequences can be severe:
- Potential lawsuits from customers whose information has been exposed
- Ransomware demands from attackers
- Recovery costs – for example, restoring or patching systems that have been breached
- Reputational damage and loss of customers
- Fines or penalties from regulatory bodies (depending on the industry)
- Downtime while data is recovered
For individuals whose data has been breached, the main consequence is that it could lead to identity theft, causing financial loss and emotional distress.
How to keep data safe and secure
So, how to protect data from cybercriminals? There are several steps you can take to prevent criminals from stealing data. These include:
Use secure passwords
Passwords can be easily cracked by hackers, particularly if you don't use a strong password. A strong password is at least 12 characters or longer and comprises a mix of upper- and lower-case letters plus symbols and numbers. The shorter and less complex your password is, the easier it is for cybercriminals to crack. You should avoid choosing something obvious – such as sequential numbers (“1234”) or personal information that someone who knows you might guess, such as your date of birth or a pet’s name.
To make your passwords more complex, you could consider creating a 'passphrase' instead. Passphrases involve picking a meaningful phrase that is easy to remember and then making the first letter of every word the password.
Avoid using the same password for multiple accounts
If you use the same password for multiple accounts, if a hacker cracks your password on one website, they also have access to many more. Remember to change your passwords regularly – every six months or so.
Avoid writing down your passwords
Writing a password down anywhere leaves it susceptible to being found by hackers, whether it’s on a piece of paper, in an Excel spreadsheet, or in the Notes app on your phone. If you have too many passwords to remember, consider using a password manager to help you keep track.
Multi-factor authentication
Multi-factor authentication (MFA) – of which two-factor authentication (TFA or 2FA) is the most common – is a tool that gives internet users an additional level of account security beyond the standard email address/username plus password combination. Two-factor authentication requires two separate, distinct forms of identification to access something. The first factor is a password, and the second commonly includes a text with a code sent to your smartphone or biometrics using your fingerprint, face, or retina. Where possible, enable multi-factor authentication on your accounts.
Be cautious when sharing personal information
Try to keep access to your data on a 'need to know basis, both online and offline. For example, if someone is asking for your personal information – such as your Social Security number, credit card number, passport number, date of birth, work history or credit status, etc. – ask yourself why they need it and how they will use it. What security measures do they have in place to ensure your private information remains private?
Limit social media sharing
Familiarize yourself with each social networking platform’s security settings and ensure these are set to a level you are comfortable with. Avoid disclosing personal information like your address or date of birth in your social media bios – criminals can use this data to build up a picture about you.
Close unused accounts
Most of us have signed up for online services that we no longer use. Where those accounts still exist, they likely contain a mix of your personal data, identity details, and credit card numbers – all valuable information for cybercriminals. Worse, if you use the same password for multiple accounts – which is definitely not recommended – then a password leak at one site can mean attackers obtain access to your accounts at other sites. To protect your privacy, it’s advisable to remove your private data from services you no longer use. You can do this by closing those outdated accounts rather than leaving them dormant.
Shred personal information
Shred letters which contain personal details like your name, date of birth, or Social Security Number. Keep an eye on your mail, as this could alert you to a data breach that may have gone undetected. For example, if you receive documentation related to a doctor’s visit you didn’t attend, it could be a sign your data has been breached, and it's time to take action.
Keep systems and programs up to date
Keep all operating systems and software programs up to date by regularly installing updates to security, web browsers, operating systems, and software programs as soon as they become available.
Monitor your accounts
Regularly check your bank or credit card statements, or other accounts, so you can see if any unauthorized charges or other anomalies have taken place. You may not receive a notification when a company you transact with has a data breach, so it's advisable to stay vigilant yourself.
Be wary of free Wi-Fi
Using free public Wi-Fi has become a daily routine for many people, but secure and reliable connections are not always what they seem. Public Wi-Fi hotspots can be easy targets for hackers and cybercriminals who can use them for data stealing. To stay safe on public Wi-Fi, avoid opening or sending sensitive data, turn off Bluetooth and file sharing, use a VPN and a firewall. A good antivirus is also essential. Read our tips on how to stay safe using public Wi-Fi here.
Stay informed
Keep an eye on the news in general or monitor security news websites to be sure you hear about it when a company you interact with suffers a data leak or data breach.
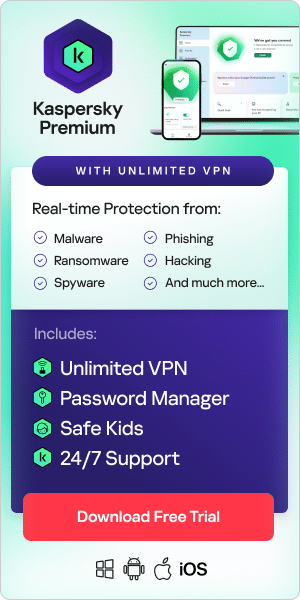
One of the best ways to stay safe online is by using a high-quality antivirus. Kaspersky Total Security works around the clock to secure your devices and data. It locates device vulnerabilities and threats, blocks cyber threats before they take hold, and isolates and removes immediate dangers.
Related articles: