Is the Internet A Threat to Privacy?
Data is worth money, which is a major reason that your online privacy is under threat.
For instance, knowing your browsing habits or search history can deliver big profits to advertisers. If you've been searching for new apartments, your search history could tip an advertiser off to the fact that you're going to be moving home soon — time to start serving you ads for moving services, furniture, DIY stores, and home insurance.
While that's a legitimate use of your data, personal data is also worth money to criminals: credit card details are openly sold on the Dark Web. If a hacker can manage to get unauthorized access to an airline's reservation system or an e-commerce site's customer database, they've hit the jackpot.
Any information you put on the web might be used maliciously. Therefore, you must be careful about your online privacy. Let's look at why internet privacy matters, and how you can help protect your privacy online.
What Is Internet Privacy, and Why Does It Matter?
Privacy breaches on the internet pose real dangers. For instance, your medical conditions could be shared without your consent, or your banking data could be made available to third-parties. You might have your emails hacked. Your identity could be stolen.
The risks are more far-reaching than most people realize because of what might happen to your data next. The development of Big Data means that your browsing history could be analyzed to come up with conclusions that you don't want to be drawn. For example, a woman buying items such as folic acid supplements and unscented moisturizers might not appreciate a marketing agency identifying her as 'pregnant' and targeting her with pregnancy products.
If she's living with mom and dad or hasn't told her partner, she might not be happy to see 'Congratulations on Your Baby!' marketing materials arrive in the mail.
That's just one example of how internet privacy issues go much further and deeper than just protecting your banking account details or your social media account. Whenever you visit a website or download an app, data is being stored about you — possibly without your consent and even without your knowledge. You likely want to know where that data goes and how it's used, or you could decide you want to avoid it being collected altogether.
How to Protect Your Privacy Online - Communications
One way you can protect your online privacy is to ensure that your communications are secure. Whether you're searching the web, sending an email, or using a GPS app on your phone, you're exchanging data with a server, and you need to protect that data while it's in motion.
One fundamental step in ensuring your online privacy and security is to make sure that your communications are secure. If you're at home, make sure your router is secured by a strong, hard-to-guess password. It's also a good idea to change your home network's username. Often, usernames include the name of your ISP or the router's manufacturer - this information could make a hacker's life easier. If you're using a home Wi-Fi network, use WPA authentication to ensure no one can piggy-back off your network.
Now that so many cafes, hotels, and public places have free Wi-Fi, it's tempting to log on wherever you are. But be careful; public Wi-Fi is a big security risk. If it doesn't include secure authentication, it's easy for you to log on, but it's equally easy to be targeted by a hacker. Don't use public Wi-Fi for banking transactions or other particularly sensitive internet use.
You might consider using a Virtual Private Network (VPN). How does a VPN prevent hacking of your Wi-Fi signal? It sets up a private gateway between you and the internet, encrypting your communications so that no one can see what you're doing. Even though you're using public Wi-Fi, a VPN gives you the same security you'd have on your network.
If you're carrying out any sensitive transactions, make sure you're dealing with a secure browser using HTTPS and not just HTTP. A basic HTTP website can be hacked with a 'listening' program that can log any information you're sharing. This could be your online banking username and password, for instance.
The secure HTTPS protocol uses SSL/TSL to encrypt your communication. Put in non-technical language, it creates a digitally secured environment in which you and the browser can communicate without anyone overhearing you. It's like a secure handshake between you and the website. If you're using SSL, you'll see a padlock in your browser address bar, and the website name will begin with https, not just http. Click on the padlock if you want to see details of the site's certificate.
Some online messaging services are easy to eavesdrop on. If you use Facebook, your messages aren't secure unless you use the 'Secret Conversation' facility accessed through Messenger's main menu (this is only available if you're logged in on an iPhone or Android device, not on a PC). WhatsApp and Viber, on the other hand, are encrypted end-to-end, so they're much safer to use.

How to Protect Your Privacy Online - Don't Be Tracked
Even if your access is secure, Google or another internet entity could be tracking your web use, or your ISP could be tracking you. In fact, in many countries, your ISP is required to do so, so that search histories can be made available to law enforcement if needed. So, when you're thinking about protecting your privacy online, you should think about how to prevent being followed around the web.
One way to stop Google and other organizations tracking your browser history is to use a private browsing mode. That's Incognito mode if you're using Chrome, or Private if you're using Firefox. If you're using a shared PC or using someone else's PC as a guest, using private browsing means your login credentials won't be stored on the computer (plus your friend won't end up getting targeted ads meant for you).
You can also download browser extensions that will prevent you from being tracked by the use of cookies, which will stop sites loading intrusive, targeted ads. Be careful that you only use extensions from reputable organizations - hackers have been known to create malicious software masquerading as security-enhancing apps and extensions.
Your search history might still be held in the Google server, though. Understanding your search history and using it to show you personalized ads is one-way Google makes its money. If you're not happy with this and want to tighten up your online privacy settings, then try using another search engine.
However, your ISP can still see your activity. If you’d prefer that not to happen, then this is another time you might want to use a VPN. Does a VPN prevent hacking your communications? Yes. Does a VPN also stop your ISP from seeing what you do? Yes. It uses the same method for both. Your communications are encrypted, and your ISP doesn't have the encryption key; all it can see is a stream of gibberish. Plus, you can't be tracked by web cookies or other tracking methods because the VPN will also mask your IP address. Therefore, no one can see where your communications are coming from.
Finally, remember to log off your accounts when you're not using them. Just closing the tab or even the browser isn't enough. Facebook, for instance, tracks users even when they don't have Facebook open in their browsers. To stop it tracking where you go and what you do, you need to log out. And it goes without saying that if you're logged on to a bank or a brokerage account, you should log off properly.
How to Protect Your Privacy Online - Choosing What You Put Online
You don't have to put everything online. There may be aspects of your life that you don't want everyone to know, for entirely innocent reasons. For example, some people find their middle names embarrassing or just have particular leisure interests they don't want to share in their workplace. You can protect your privacy online by thinking carefully about what you want to put online, and who you'd like to be able to see it.
It's worth thinking about whether the personal information you put on social media has any security ramifications. Internet security issues are also real-world security issues. For instance, letting people know you're having a great time at Disneyland might be quite natural, but it's information a burglar would be very happy to find out. If bank security questions include your mother's maiden name, first car, or your pet's name, keep those bits of information off your social media links.
Look carefully at what information different social media platforms make available automatically, such as your location or who you are with. Many people don't realize the 'about me' fields contain a lot of the information criminals need for successful identity theft or that could be used for a social engineering exploit. Have you made your date of birth public, so your friends know when your birthday is? That's another piece of information your bank and other sensitive accounts often use as an identifier. Explore the privacy settings of your social media accounts to control what others can see on your profile.
If you use LinkedIn, you might not realize its 'activity' section lets everyone see what you've been doing. That includes letting your employer see that you've been researching and following a couple of other companies; if you're looking for a job elsewhere, it's no longer a secret anymore! Uncheck the 'activity' setting if you don't want everything you do on LinkedIn to be public.
Many savvy Facebook users now limit their posts to 'friends only.' However, if you change a post to 'public,' perhaps because you've shared a link to an election campaign that you want your friends to be able to share, that permission might now be applied to all your future posts. Check that 'friends only' is still your default.
While we're talking about friends, are you sure you know everyone who's a Facebook friend? Should you still be friends with that person you met on vacation five years ago but haven't seen or heard from since? You can change your Facebook settings to protect yourself from hackers sending fake friend requests - restrict friend requests to 'friends of friends' to reduce your chances of being targeted.
You might also not want your email address and phone number to be available to the public via your social media profiles. Restrict your contact details to 'friends only' or even make them completely private. At the same time, you might want to turn off search engine indexing. That means if someone does a Google search on your name, they won't be able to see all your Facebook posts.
There's no privacy without security
Online privacy and security go hand in hand. We've already talked about how you can protect your communications with the internet, but you also need to protect the devices that you use for access, whether those are laptops, PCs, smartphones, or tablets.
Here are some good tips for how to ensure your devices are secure:
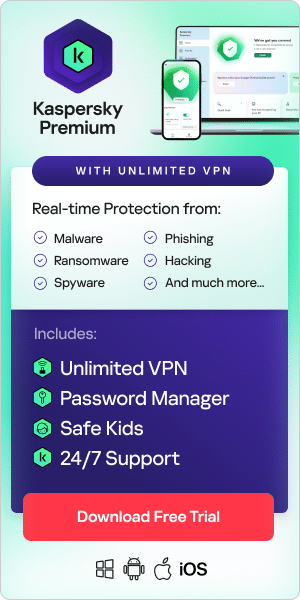
- Install trusted antivirus and antimalware software. Anti-hacker software will ensure that your devices are secured against common threats, such as keyloggers, ransomware, and Trojans. We recommend Kaspersky Total Security for the most comprehensive protection against hackers and malware.
- Ensure you regularly update your operating system and other software, particularly when security patches are issued. Hackers often use vulnerabilities in outdated software as a way to break in - don't give them the opportunity. (Note: if you're using an operating system that's no longer supported, like Windows 7, whose support ended in January 2020, you ought to replace it; it's a sitting target for hackers.)
- Be careful what you click on. Hackers often go 'phishing' by sending fake emails that purport to be from your bank or from eBay but go to a different site to steal your login credentials. Read the email address carefully, view the page source, and hover your mouse over the links to see where they go. Other phishing attempts aim to get you to click on a link to a photo or news story but load malware on your device when you do so.
- Make sure you protect your smartphone. Use the screen lock and PIN to protect it from unauthorized access. Don't jailbreak or root it - that can give hackers a way to overwrite your settings and install their own malicious software. It's a good idea to download an app that can allow you to delete all the data on your phone remotely: if your phone is stolen, you can delete your information easily.
- When you download apps, check out what permissions they require. An app that requires access to your camera, microphone, location services, calendar, contacts, and social media accounts is a potent threat to your online privacy. Famously, Pokémon Go! demanded permissions that gave it, in effect, the right to see and modify pretty much everything in your Google account except the password. This problem was quickly fixed with an update limiting the permissions required.
- Delete data, programs, and accounts that you don't use anymore. The more programs or apps you have running, the greater the chance that one of them could be compromised.
- Use strong passwords to secure your devices, internet access, and accounts. The best password managers will even create a totally randomized, ultra-strong password for each of your accounts. But whatever you do, don't lose the master password for your password manager.
- Changing your passwords every six months or so can also help reduce the chances of your accounts being hacked.
- Protect your online privacy and security by using two-factor authentication as much as you can. This allows you to enhance your security by demanding a second form of ID verification besides your passwords, such as an SMS code sent to your phone, a fingerprint, or a security dongle/fob that you can plug in via USB.
Monitor Your Privacy for Any Breaches
You may have done a good job protecting your internet privacy, but the company responsible for looking after your privacy at the other end also needs to do its job. And sometimes, security is breached, and customers' personal data gets out or gets destroyed. Although companies will generally have crisis management plans enabling them to run a customer communications campaign and set things right if there's a breach, there are several things you can do to keep yourself well protected.
First, make sure that you monitor your financial accounts regularly. Note any unexpected transactions or withdrawals and question them; they may be innocent - a direct debit that's been processed a month late, for instance - but they might also reveal that your account has been compromised.
Check your credit reports too. If your details have been used for the purpose of identity theft, your credit report will show if anyone has been trying to apply for credit in your name. This won't cost you a penny if you're smart, since each of the three credit agencies (Equifax, Experian, and TransUnion) must give you one free report every 12 months.
The moment you hear of a data breach that might affect you, change the password on that account. You might want to change the passwords on other accounts too, particularly if they're similar to the password used on the compromised account. Change any answers to your security questions, even if you must fabricate a new maiden name for your mother and a new name for your first pet. Or use a secure password manager, which helps to keep your passwords in one place, as well as protect them.
Don't respond to emails from a company saying there's been a breach and asking you to use the link in the email to change your credentials, or to phone a number. These could be phishing attempts. Instead, use the company's own website, or phone a number you already have for the company, to ascertain whether there actually has been a breach.
Related articles: