
Keeping e-sports clean
Cheats for multiplayer games are tantamount to malware, and their use in competitions to cybercrime.
519 articles

Cheats for multiplayer games are tantamount to malware, and their use in competitions to cybercrime.


Eugene Kaspersky explains how Kaspersky Sandbox uses virtual machines to thoroughly examine malware’s behavior.

To build a safer future, we need to stop fearing and start immunizing.

Workers who are comfortable storing work information on their personal devices are not always cautious enough to keep it secure.



Digital signatures cannot solve the requirement of checking the authenticity of documents required by KYC procedures. That is where smart contracts may come in handy.

For three weeks, Baltimore’s administration has been struggling with the aftermath of a ransomware attack.

To protect themselves, businesses need to take a proactive approach, constantly adapting their security controls to the ever-changing threat environment.

It appears the ASUS incident was just one part of the large-scale operation.

Trojanized HID devices as well as surveilling or malicious cables are serious threats that can be used to compromise even air-gapped systems.

A new APT attack targets the diplomatic mission of an Asian country.

A cybergang that specializes in cyberespionage, with its campaign mostly limited to the Middle East and countries in central Asia.

Our technologies detected a threat that seems to be one of the biggest supply-chain attacks ever.

A new strain of Mirai is equipped with a much wider range of exploits, including some targeted at enterprise-class IoT devices.

Do not expect data encrypted by ransomware to be restored easily. It is better to protect the data in the first place.

The hidden dangers of out-of-office messages.

Mobile World Congress 2019 recapped: 5G, Internet of Things, ultrasonic fingerprint sensors, and artificial intelligence.
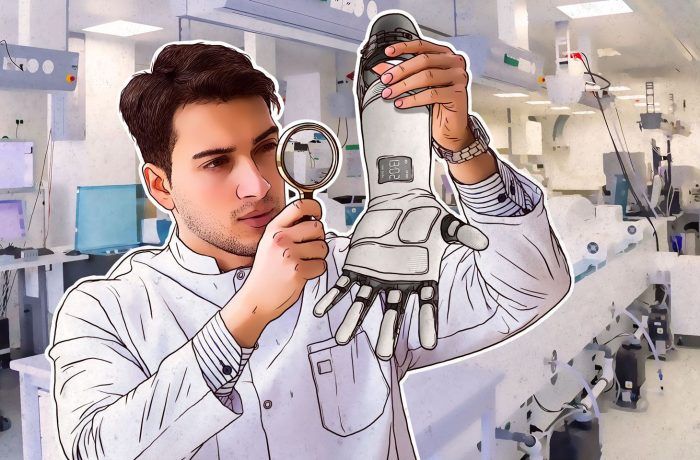
At Mobile World Congress 2019, our experts presented a study on the security of Motorica smart artificial limbs.