While this post comes out on April 1, the threat described has little to do with April Fools’ Day — except for the fact that the CrystalX malicious RAT, discovered by Kaspersky experts, can do more than just gain remote access to a victim’s device, steal cryptocurrency and credentials from browsers and apps, or conduct actual surveillance. It can also flip the victim’s screen, swap mouse buttons, write nonsense directly onto the screen, and even block keyboard input. Furthermore, it’s advertised as malware-as-a-service (MaaS) — meaning it’s subscription-based — on Telegram and through instructional videos on YouTube.
In this post, we explain some basics as to how this new malware was built, what makes it difficult to detect, and what to do so you don’t end up among its victims.
A Swiss army knife for attackers
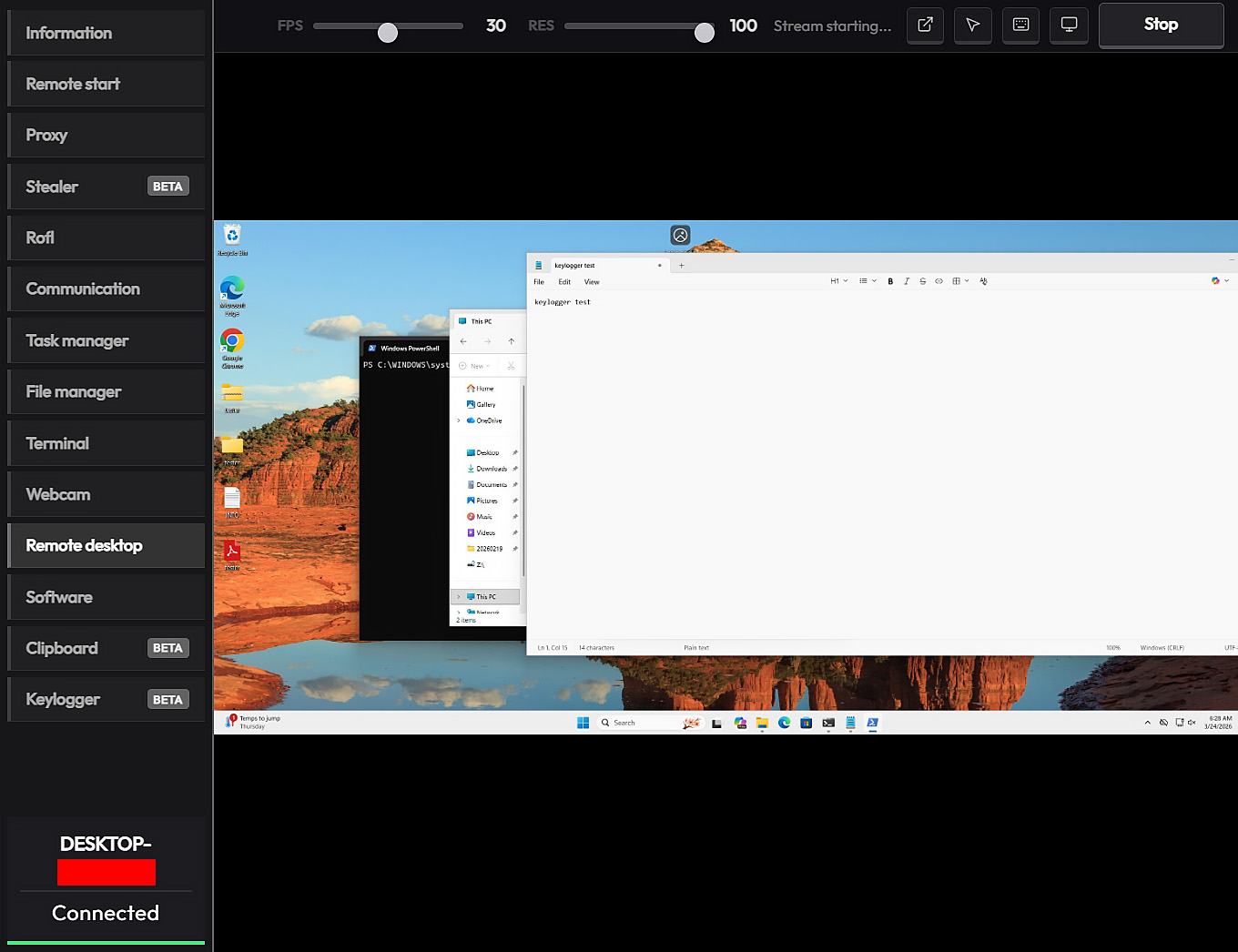
In March 2026, our experts discovered previously unknown malware circulating on private Telegram channels. Borrowing from classic marketing tactics, the Trojan was offered for purchase via three different subscription tiers. Its capabilities cover a fairly broad spectrum: judge for yourself what it can do to a victim’s computer:
- Change desktop wallpaper to an image from a specified link
- Rotate the screen by 90, 180, or 270 degrees
- Simply shut down the computer
- Swap mouse button assignments
- Chat with the victim
- Block both keyboard input and monitor output
- Display any notification text chosen by the attacker
- Disable specific components, such as Task Manager, the command prompt, and the Windows taskbar
Yet that’s only the harmless side of the malware — the prank functionality that harks back to the joke viruses of past decades. The real damage from CrystalX comes from its stealing login credentials for Steam, Discord, Telegram, and all Chromium-based browsers. It can also monitor and change the contents of the clipboard; typically, attackers watch for a crypto wallet address to be copied, and then swap it with their own. This is a popular scheme for stealing crypto: while intending to make a legitimate transfer, the victim copies the recipient’s wallet address, but ends up pasting the scammers’ address instead.
But there’s more: a keylogger feature and full device control with remote access to the screen, camera, and microphone — including video and sound recording capabilities.
The malware was first mentioned in January 2026 in a private Telegram chat for RAT developers. At that time, this Windows Trojan was called WebCrystal RAT and, based on technical details, was revealed to be a clone of another RAT known as WebRat. A short time later, the author of WebCrystal rebranded it as CrystalX RAT, and began touting the Trojan on a newly created Telegram channel.
The initial infection vector for this stealer is currently unknown, but according to telemetry the victims at the time of writing are predominantly located in Russia. And since we’re continuing to find new versions of the malware, we deem it a rapidly growing and evolving threat.
Anyone can become a hacker
Developing any complex cyberattack used to come with a steep learning curve. You needed to understand cryptography and network protocols, and know how to write code that could fool antivirus solutions. It was a high bar to clear, but the malware-as-a-service model has been changing the game.
These days, an attacker only needs basic computer literacy to rent a ready-made platform with a user-friendly user interface. The threat is becoming widespread specifically because malware creators aren’t carrying out the attacks themselves anymore — they’re selling shovels during a gold rush. They focus on supporting their customers, improving the user interface, and pouring money into aggressive marketing.
Hackers are even setting up YouTube channels where they use the pretext of “for educational and entertainment purposes” to explain how to manage the Trojan from the control panel. Instructional videos that were once buried in the dark web have gone mainstream, putting hacking techniques in front of a broad, general audience.
How CrystalX bypasses security
No matter how technically advanced a hacking app’s code is, it will die as a project without a constant stream of new clients. This makes marketing efforts vital to its survival — even if they significantly increase the risk of the developer ending up behind bars. However, the creators of CrystalX have figured out how to protect their creation.
The control panel allows clients to build their own unique versions of the Trojan with extensive configuration options. For example, they can enable location filtering to target users in specific countries, choose an icon for the executable file, and toggle anti-analysis features. The finished Trojan is compressed using zlib and then encrypted with a ChaCha20 stream cipher using a 256-bit key and a 96-bit nonce. This ensures that every customer receives a unique version of the malware.
CrystalX is also capable of detecting virtual machines and checking if it’s running in a test or debugging environment, which complicates discovery. You can read more about the structure and functionality of this new Trojan in our Securelist story.
The good news for Kaspersky users is that our security solutions both detect and neutralize CrystalX.
How to avoid becoming a victim
Here are a few simple tips to help you avoid infection by CrystalX and other similar malware:
- Pay attention if your computer starts acting up. Spontaneous screen rotation, the keyboard or mouse behaving erratically or locking up, and random notifications or chat windows can all be signs of a CrystalX infection. If anything like that happens, kill the internet connection immediately by physically unplugging the Ethernet cable or toggling off the Wi-Fi. Then, use a flash drive to install our security suite to root out the virus.
- Make sure you download software only from official websites and trusted marketplaces. Avoid pirated software, license key generators, and free versions of paid applications: these builds are the most common hiding spots for Trojans.
- Don’t fall for “tutorial” videos that push questionable tools for “administration”, “optimization”, or “security testing”. If the blogger says you should disable your antivirus to complete installation, that’s a major red flag and a reason to stop watching.
- Be careful with files you receive through messaging apps. Password-protected archives containing “important documents” or “cool private builds” are typical containers for malicious software.
- Keep your accounts secure. Enable two-factor authentication and passkeys for your most critical services: email, messaging apps, gaming platforms, and crypto exchanges. Kaspersky Password Manager is an excellent tool for this.
- Regularly update your operating system and apps. Fresh patches plug security holes that let malware slip onto your system silently and without any interaction from your side.
- Use a reliable security suite, such as Kaspersky Premium. It detects and blocks Trojan installation or download attempts.
Read more about remote access Trojans, miners, crypto-stealers, and other digital nasties:
 RAT
RAT

 Tips
Tips