The entire series of The Сyberworld Survival Guide can be found here: https://www.kaspersky.com.au/blog/tag/securityIS
The man in the sunglasses already knows whose ID he will use tomorrow to cross the border.
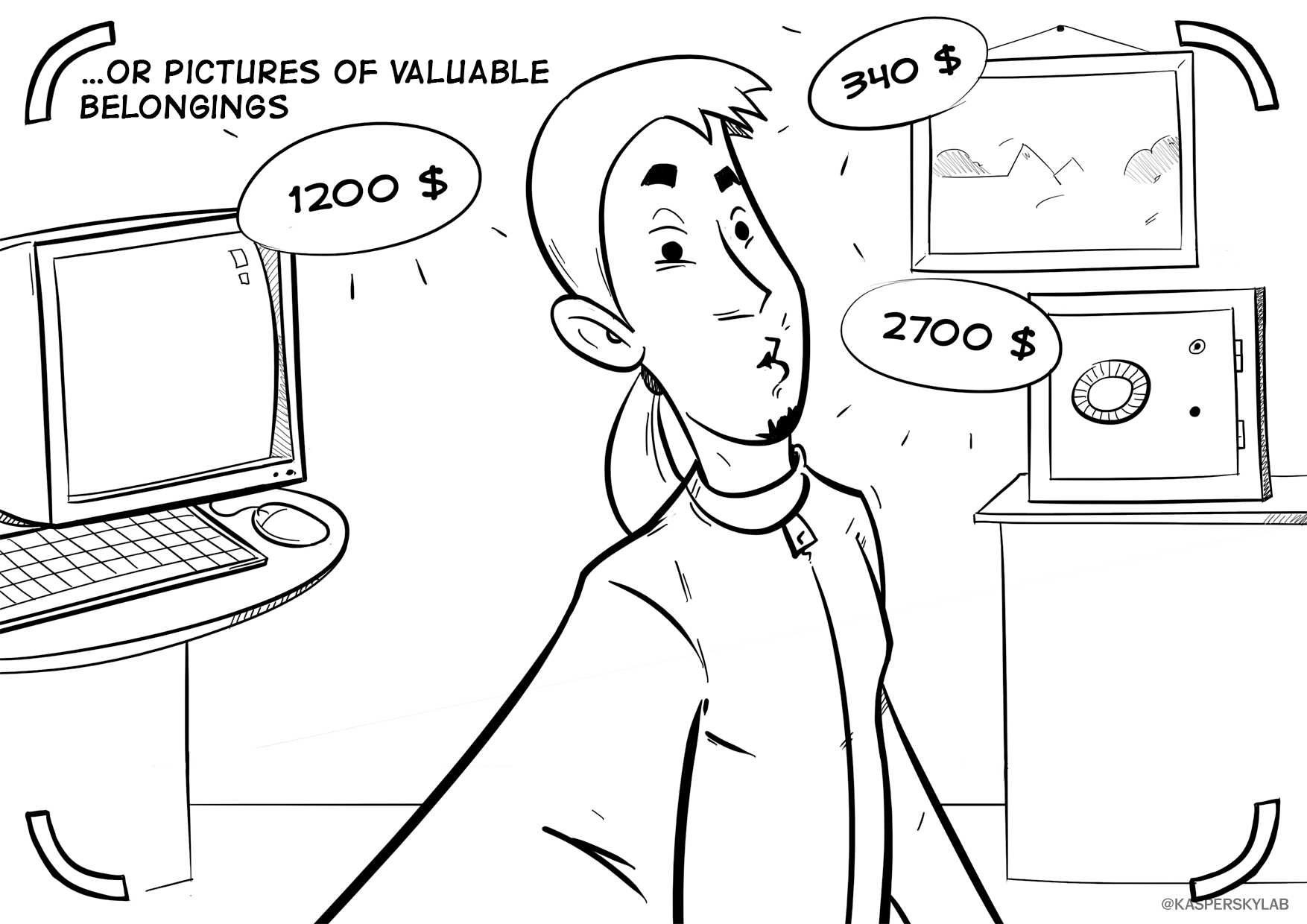
At least don’t leave huge price tags on your belongings.
 SecurityIS
SecurityIS