The next page of The Сyberworld Survival Guide. The entire guide can be found here: https://www.kaspersky.com.au/blog/tag/securityIS
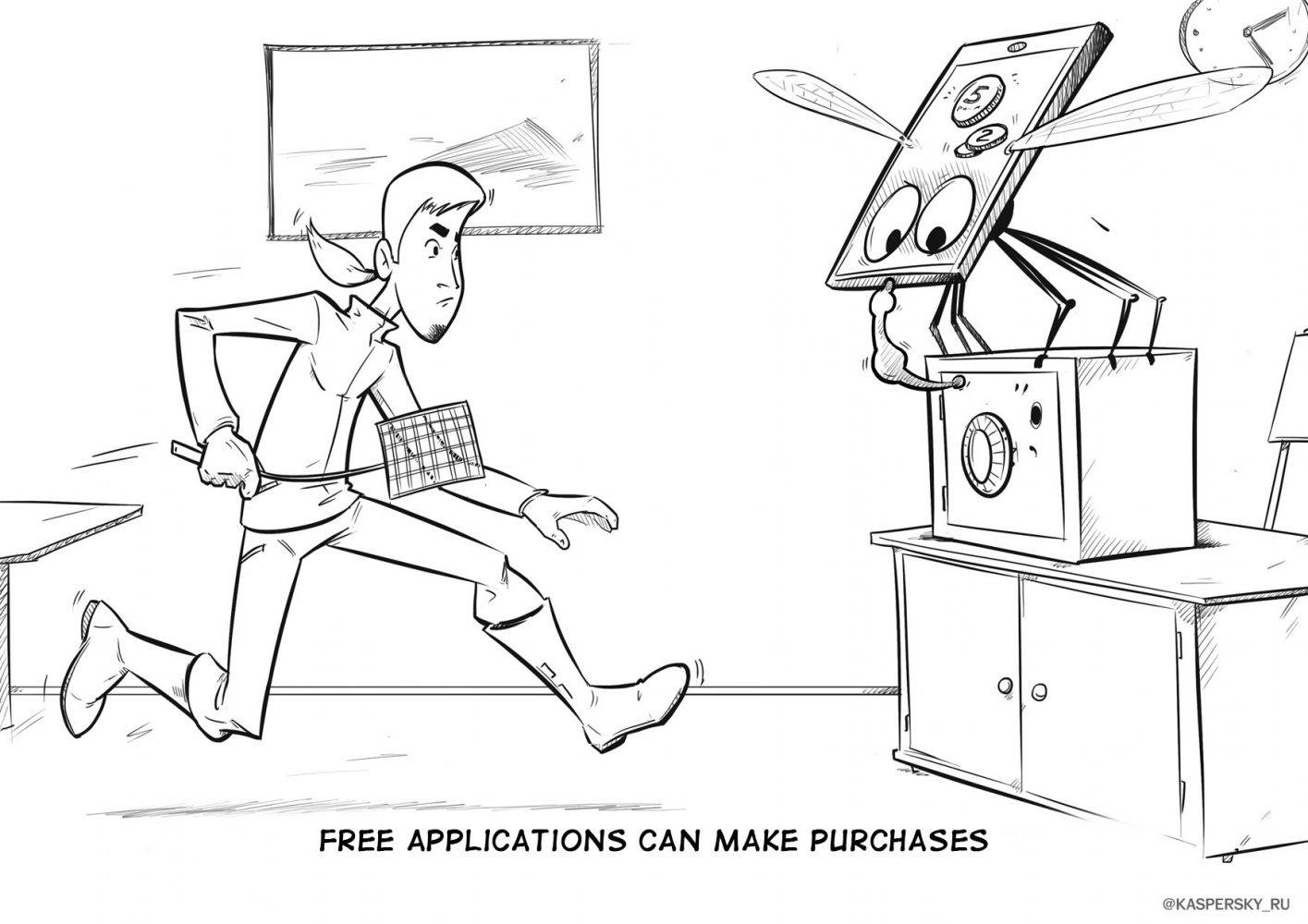
The breeding experiment with a mosquito and a tablet was considered a failure.
The next page of The Сyberworld Survival Guide. The entire guide can be found here: http://www.kaspersky.com.au/blog/tag/securityIS
The next page of The Сyberworld Survival Guide. The entire guide can be found here: https://www.kaspersky.com.au/blog/tag/securityIS
The breeding experiment with a mosquito and a tablet was considered a failure.

It’s getting harder and harder to spot fraudulent online retailers as more and more websites peddling discounted good emerge in the already crowded field of Internet merchants.

We break down the BeatBanker trojan attack, which combines espionage, crypto theft, and mining with inventive ways to dig its heels into a smartphone.
A browser-in-the-browser attack, theoretically described in 2022, has been adopted in real-world phishing. We break down how it works, and how to spot a fake authentication window.
What is the year 2038 problem — also known as “Unix Y2K” — and how to prepare corporate IT systems for it?
Eight digital New Year’s resolutions you absolutely need to keep.